Research Platform
KSI-Forge
Compliance Duration Analytics for Regulated Cloud Environments
A patent pending prototype that validates not just whether security controls have been implemented, but how long they have been maintained in a compliant state.
Request a BriefingThe Problem with Point-in-Time Compliance
Assessment reports confirm a control's status at the time of evaluation. They do not capture what happened between assessments.
Configuration Drift
Cloud security controls become non-compliant between assessments due to infrastructure changes, personnel transitions, or routine operations. GRC teams need real-time visibility into compliance duration and control effectiveness.
Just-In-Time Compliance
Controls become compliant right before the next audit to pass an assessment despite having been non-compliant for weeks or months. Point-in-time snapshots cannot distinguish sustained compliance from last-minute remediation.
Shared Risk Exposure
Federal agencies share cloud services through the FedRAMP "authorize once, reuse many" model. When a CSP's controls degrade, every consuming agency is exposed. GRC teams lack continuous compliance visibility to validate whether shared cloud services have remained compliant since the last authorization.
Temporal Blind Spot
NIST SP 800-137 defines the federal approach to continuous monitoring, but it does not address how long a security control has actually been maintained in a compliant state. This is the gap KSI-Forge addresses.
A Different Approach
KSI-Forge adds compliance duration as a measurable dimension. Beyond PASS or FAIL, Authorizing Officials, 3PAOs, and Cloud Service Providers see how long controls have remained compliant, how long they were non-compliant, and whether compliance was achieved just in time for assessment.

KSI-Forge prototype validation: Two controls show PASS status but were non-compliant for 64 days before achieving compliance 13 days ago. Both are flagged as Just-In-Time Compliance risks with an assessor alert.
Three Novel Capabilities
Each capability is the subject of a provisional utility patent filing (Application #63/995,503), the first in compliance duration analytics.
Compliance Duration Engine
Rather than recording whether a control passes or fails, the system calculates how long the control has been in its current state. It produces an objective temporal measure of compliance that cannot be manipulated by last-minute remediation.
Just-In-Time Detection
The system classifies each control into tiered severity levels based on how recently the compliant state was established. Controls with short compliance durations are flagged as potential JIT risks. Controls sustained over longer periods are classified as stable.
Multi-Cloud Normalization
Federal agencies consume services across AWS, Azure, and GCP, each with different infrastructure models. KSI-Forge normalizes compliance duration metrics across all three providers into a unified framework for consistent measurement.
Cloud Agnostic Design
KSI-Forge validates controls natively across all three major cloud providers. No agents, no proxies, no control-plane modifications.
Risk Framework Agnostic by Design
Prototype coverage spans 10 risk frameworks with more than 40 validators across native cloud controls. The architecture supports expansion to additional frameworks without structural changes.
Enterprise Integration
Compliance duration metrics flow into the platforms your teams already use for risk management, incident response, and executive reporting.
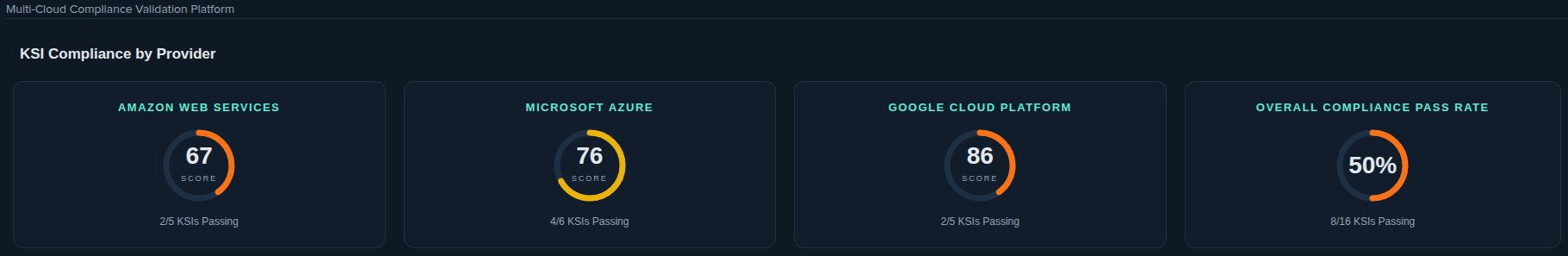
KSI-Forge compliance scores by cloud provider with per-platform KSI pass rates and overall compliance visibility
GRC Platforms
Compliance duration data structured for export to governance, risk, and compliance tools for unified risk management and audit preparation.
ITSM Systems
Duration metrics formatted for IT service management workflows to support automated ticketing and remediation tracking.
SIEM Tools
Compliance duration logs structured for executive dashboards, alerting rules, and correlation with security event data.
Current Prototype Status
KSI-Forge is a functional prototype, not a concept. Here is what has been built and what remains to be validated.
Demonstrated
Requires Validation
Trust and Transparency
Architecture principles that ensure KSI-Forge earns trust from engineering, security, and assessment teams.
Read-Only by Default
Scoped API permissions with zero write access to production, staging, or development environments.
API-Driven
All data ingestion through native cloud provider APIs. No agents, no proxies, no sidecar processes.
Transparent Lineage
Every evidence artifact traces back to the source control signal. Full chain from cloud resource to compliance finding.
Assessor Independence
Evidence packages designed for assessor review, not assessor replacement. KSI-Forge does not attest or certify.
Clear Boundaries
Will Do
Won't Do
Built For
GRC Team / Compliance Manager
Build a defensible program maturity narrative that is repeatable, measurable, and evidence-backed.
CISO / Executive Sponsor
Board-safe risk narrative with continuous visibility into control health. Reduce executive exposure and audit surprise risk with leading indicators, not post-mortems.
CTO / Platform Engineering
Fewer ad-hoc evidence requests and engineering interruptions. Earlier drift detection reduces last-minute remediation crunch without introducing operational risk.
3PAOs / Assessment Organizations
Cleaner evidence, clearer lineage, and fewer surprises. Optional read-only evidence views and exportable, time-stamped packages that preserve full assessor independence.
Learn How KSI-Forge Measures Compliance Duration
Whether you are exploring research partnerships or want to understand how compliance duration analytics works, we welcome the conversation.
Request a BriefingKSI-Forge validates operational control signals across cloud-native security implementations. It does not claim authorization or certification, and does not replace assessor judgment.